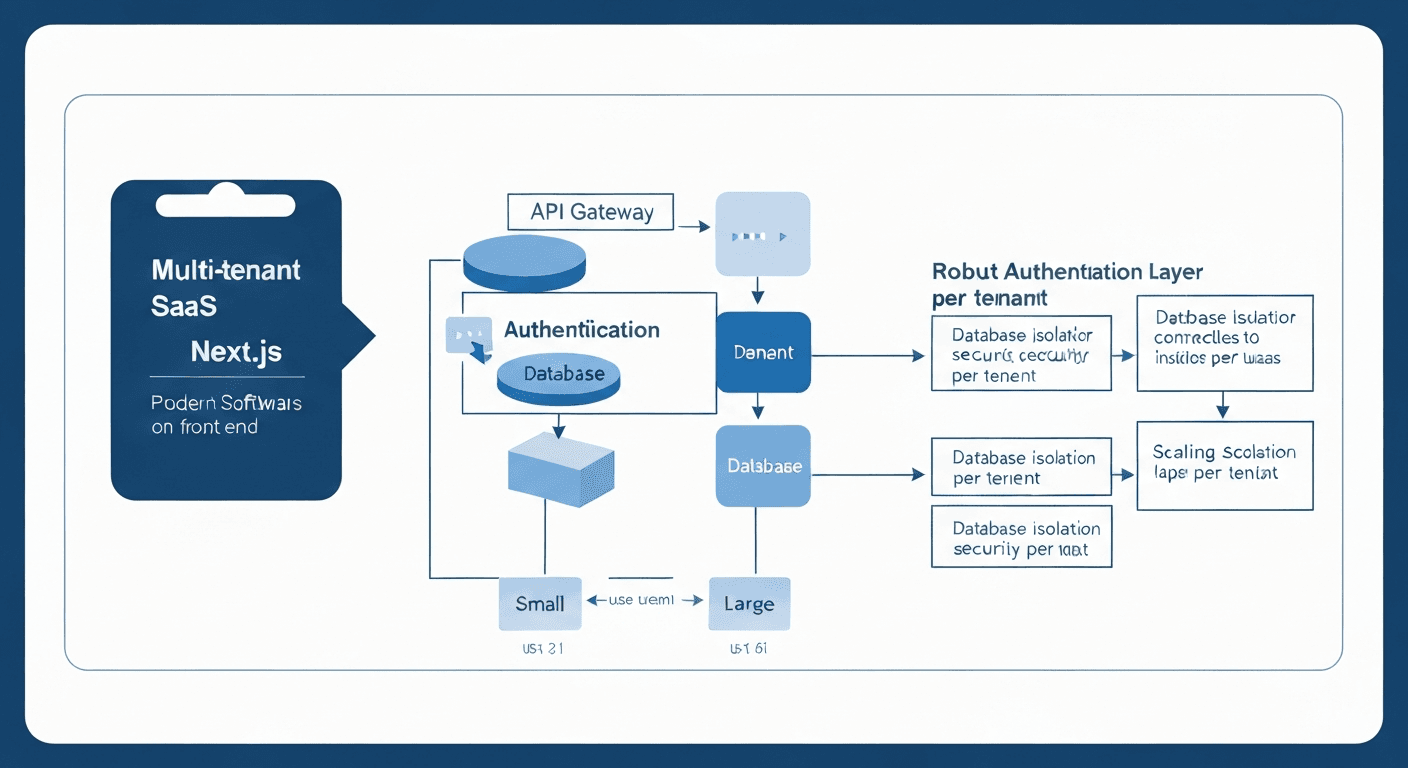
A multi-tenant SaaS authentication system built with Next.js requires careful architecture from day one to handle growth from your first 10 customers to thousands of small businesses. The key is implementing proper tenant isolation, choosing the right database strategy, and building authentication flows that scale horizontally without performance degradation.
I’ve architected systems that started with a handful of small business clients and scaled to serve tens of thousands. The difference between systems that break at 500 users and those that gracefully handle 10,000+ comes down to three foundational decisions made early.
Why Multi-Tenant Architecture Matters for Small Business SaaS
Small businesses have unique requirements that make multi-tenancy essential. They need data isolation, custom branding, and role-based permissions within their organization. But they also expect fast performance and competitive pricing.
Single-tenant architectures become prohibitively expensive around 100-200 customers. You’re essentially running separate infrastructure for each client. Multi-tenant systems share resources efficiently while maintaining strict data separation.
The challenge? Building tenant isolation that’s bulletproof from the start.
Database Strategy: Tenant Isolation That Actually Works
Your database strategy determines everything else. I recommend the hybrid approach: shared database with tenant-specific schemas for each organization.
Here’s the structure that’s worked consistently:
- Master tenant table: Stores organization metadata, subscription info, and routing data
- Tenant-specific schemas: Each organization gets its own schema within the shared database
- Shared tables: User authentication, audit logs, and system-wide data remain in the main schema
This approach gives you the cost benefits of shared infrastructure with the security of true data isolation. When TechCorp logs in, they only see data from the techcorp schema. Never mixed with data from other tenants.
Implementation with Prisma and PostgreSQL
PostgreSQL’s schema feature makes this straightforward. Each tenant gets a schema like tenant_abc123, and your Prisma client switches contexts based on the authenticated user’s tenant ID.
The connection string becomes dynamic: postgresql://user:password@localhost/saas_db?schema=tenant_${tenantId}
This scales beautifully. I’ve seen systems handle 5,000+ tenants on a single database instance without breaking a sweat.
Next.js Authentication Flow: Multi-Tenant Session Management
Standard authentication libraries weren’t built for multi-tenancy. You need custom middleware that validates both user identity and tenant access on every request.
The authentication flow looks like this:
- User logs in with email/password
- System looks up which tenants this user belongs to
- User selects their organization (or auto-selects if they only belong to one)
- JWT token includes both user ID and tenant ID
- Every API route validates tenant membership before processing
Your Next.js middleware becomes the security gatekeeper:
“`javascript
export function middleware(request) {
const token = request.cookies.get(‘auth-token’)
const { userId, tenantId } = verifyToken(token)
// Validate user belongs to this tenant
if (!validateTenantMembership(userId, tenantId)) {
return NextResponse.redirect(‘/unauthorized’)
}
}
“`
This runs on every protected route automatically. No possibility of cross-tenant data leaks.
Scalable SaaS Architecture: Performance Under Load
Small business SaaS systems experience unpredictable traffic patterns. One client might have 5 users, another might have 500. Your architecture needs to handle both gracefully.
Connection Pooling Strategy
Database connections become the bottleneck around 1,000 concurrent users. Implement connection pooling at the application level, not just the database level.
I use Prisma’s connection pooling with these settings for small business workloads:
- Max connections: 20-30 per instance
- Timeout: 10 seconds
- Connection lifecycle: 1 hour max
This configuration handles traffic spikes without overwhelming the database.
Caching Layer for Tenant Data
Tenant metadata gets requested constantly. Cache it aggressively with Redis using tenant ID as the key. Set TTL to 15 minutes for most tenant data, 1 hour for subscription info that changes rarely.
User permissions within a tenant change more frequently. Cache for 5 minutes max, and implement cache invalidation when roles change.
Security Considerations: Protecting Small Business Data
Small businesses trust you with sensitive customer data, financial records, and business operations. Security isn’t optional.
Row-level security in PostgreSQL adds an extra layer. Even if your application logic fails, the database enforces tenant isolation:
“`sql
ALTER TABLE orders ENABLE ROW LEVEL SECURITY;
CREATE POLICY tenant_isolation ON orders
USING (tenant_id = current_setting(‘app.current_tenant_id’));
“`
This prevents data leaks even if someone bypasses your application security.
API Rate Limiting Per Tenant
Implement rate limiting at the tenant level, not just user level. One tenant’s heavy usage shouldn’t impact others. I typically set limits of 1,000 requests per minute per tenant for small business plans.
Monitoring and Scaling Indicators
Watch these metrics to know when to scale:
- Database connection utilization: Scale up when consistently above 70%
- Query response time by tenant: Identify problematic tenants early
- Memory usage per tenant: Some tenants will have much larger datasets
Around 2,000-3,000 active tenants, you’ll want to consider database sharding or read replicas. But the architecture I’ve outlined handles that transition smoothly.
Implementation Roadmap
Start with the database schema and tenant isolation middleware. These are hardest to change later. Build your authentication system around tenant context from day one.
Add caching and performance optimizations as you grow. Monitor tenant-specific metrics from the beginning, even with just 10 customers. This data becomes invaluable when planning your scaling strategy.
The authentication system architecture that works for 10 users will work for 10,000 if you make the right foundational choices. Focus on tenant isolation, security, and clean separation of concerns. Everything else can be optimized later.
Frequently Asked Questions
What’s the best database strategy for multi-tenant Next.js applications?
The hybrid approach works best: shared PostgreSQL database with tenant-specific schemas. This provides true data isolation while maintaining cost efficiency. Each tenant gets their own schema (like tenant_abc123) within the shared database instance.
How do you handle user authentication across multiple tenants?
Implement a two-step authentication flow: first authenticate the user, then validate tenant membership. Store both user ID and tenant ID in the JWT token, and use Next.js middleware to validate tenant access on every request. Users can belong to multiple tenants but must select which organization they’re accessing.
When should I consider sharding my multi-tenant database?
Consider database sharding when you reach 2,000-3,000 active tenants or when your largest tenants start impacting performance for others. Monitor database connection utilization (scale at 70%+ consistently) and query response times per tenant as early warning indicators.
How do you implement proper tenant isolation in Next.js?
Use PostgreSQL’s row-level security policies combined with application-level middleware. Create database policies that enforce tenant_id matching, and implement Next.js middleware that validates tenant membership before processing any request. This creates multiple layers of protection against data leaks.
What caching strategy works best for multi-tenant SaaS applications?
Cache tenant metadata aggressively with Redis using tenant ID as the key. Set different TTL values based on data change frequency: 1 hour for subscription info, 15 minutes for general tenant data, and 5 minutes for user permissions. Implement cache invalidation when critical data changes.
How many tenants can a single Next.js application handle?
With proper architecture, a single Next.js application can handle 5,000+ tenants on standard cloud infrastructure. The limiting factors are usually database connections and memory usage per tenant, not the Next.js framework itself. Plan for horizontal scaling around 3,000 active tenants.